I got the opportunity to talk to Iann De Maria and Romain Pironneau earlier today about the launch of their Kickstarter campaign for an Edward Snowden inspired privacy-oriented keyboard that runs a live Linux OS. Read on to find out what got said!
Hammy Havoc: Hey guys, introduce yourselves to our readers!
Iann De Maria: Hi Hammy, we’re the two co-founding culprits behind Preevio, Iann De Maria, CEO and Romain Pironneau, CTO.
HH: Great to be talking to you today, you must be very excited about the launch of your Kickstarter campaign?
Romain Pironneau: We are thrilled indeed, two years of work finally coming to fruition! Crowdfunding is great because it puts us in direct touch with our community rather than investors and business people.
It’s riskier and more uncertain for us but much more authentic and satisfying.
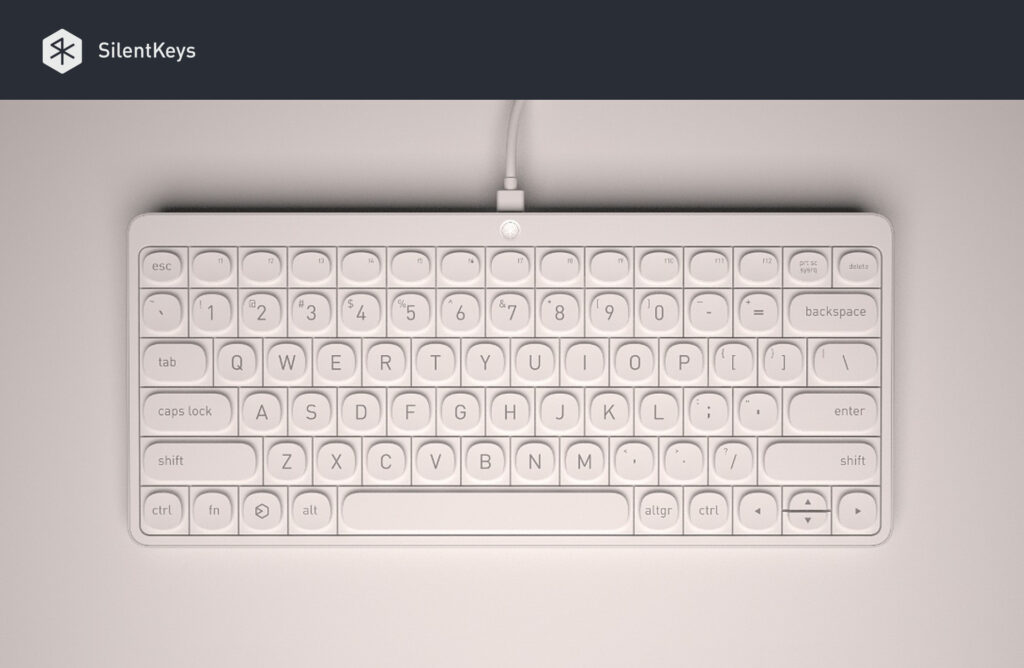
HH: So just what is SilentKeys?
IDM: SilentKeys is a software and hardware fusion of the best security and privacy solutions, designed to help people deal with today’s growing computing issues. We feel there’s a lot of fatalism surrounding privacy these days and we want to be part of the solution. Many nontechnical folks just assume that privacy is dead simply because they don’t have the time or resources to research the subject.
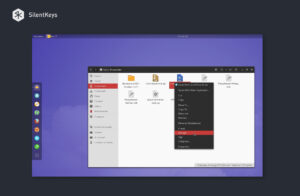
RP: We designed SilentKeys to be easy and fool-proof at various levels: the OS is a live, RAM disk based affair derived (forked) from the venerable Tails project (we’re not affiliated). This means that it can’t decay or get infected like standard installed OSes: it regeneratively loads from scratch at every use. Network management is also designed to be fool-proof: out of the box fully SSL, proxied Tor or VPN network links with an automatic Clearnet kill switch to ensure all traffic enters and leaves encrypted.
RP: OS System files and partitions are stored on a secure, hardware write-protected flash memory to ensure they’re safe from remote malware, tampering and user errors. The user’s files, settings and all of the /home partition are persistent and stored on a standard removable SD card. Fully LUKS encrypted obviously. This makes it a carry-everywhere secure vault for Bitcoin wallets, sensitive files, business secrets, passwords, private pictures and even online identities.
IDM: We’re wary of the false sense of security pitfalls and this is why SilentKeys covers much more surface and attack vectors than traditional security or privacy products. Antiviruses, Tor routers or VPN accounts fall way behind and do not secure as many layers of the privacy onion conundrum as SilentKeys does.
RP: Specifically, SilentKeys addresses data/keyboard input, OS security and integrity, app security, credentials security, local data storage encryption and network protection.
HH: What’s your background? Any other projects/products/services you’ve been associated with?
IDM: Following network and system management studies I started as sysadmin and level 2 user support on NT4 & Win2000 in a training center back in 2001. My career gave me much insight into the endpoint and the sometime surreal relationships user(s) have with it! I’ve worked for Phillips, GDF-Suez, LVMH, Jones Lang LaSalle and a government agency.
RP: Programming is the family-business and I was the local computer wizard: my first real job was installing a full cyber-cafe at the age of 14. The biggest projects I’ve participated in have been working on a large video security product and totally redesigning and rebuilding all the software solutions for an outdoor smart multimedia kiosk system, ViaDirect, as development team leader.
HH: Who runs Preevio, the company behind SilentKeys?
IDM: Romain leads software development, Julien does a crucial job on OS UX and graphic design, Bruno is our Product Designer and Samit takes care of the 2.0 marketing side of things. I do all the boring running a company stuff and oversee hardware development.
HH: Barcelona and Paris? What’s the story there? Do you collaborate remotely?
RP: We all have a very special relationship with Spain, specifically with Barcelona and Granada. SilentKeys was first prototyped in the latter while Romain, Bruno and Julien have all lived in the former. Bruno, who designed SilentKeys lives in Barcelona but the rest of us is here in Paris.
HH: Any background in pen testing?
IDM: None that we can discuss publicly. 🙂 But as I said earlier, I have extensive experience in endpoint security policies, management and their shortcomings. Romain is more experienced in crypto tools and implementation as well as code auditing.

HH: Is there something that made you so passionate about privacy and security such as having had your own compromised in the past?
IDM: Even though I’m in IT I’ll admit shamelessly: yes, I was a victim! I wrote a blogpost about the project’s genesis that tells the tale: in 2012 I was keylogged in a cybercafé in south India and it almost ruined my trip. And then on top of that came Snowden.
This really revealed the ethical aspect of it, the Big Brother fear, seeing the Panopticon incarnate right in front of us, our generation is scary. We’ve all watched the SF dystopian movies, it’s easy to see where this could end up: centralization, self-censorship and submission to various automated supra- or post-human “systems”. Silicon proto-Gods that people will assume “are so powerful and vast and all-seeing that they can’t be wrong, can’t be manipulated”. And we’re not even touching the profound social changes smartphones, IoT and social media are having on our societies. Not necessarily all bad but all deeply profound. We never expected the privacy, tracking and snooping issues to become so lawless and unregulated back when we started playing around with DX486 and Cyrixes back in the 90s. I guess the lesson is if they can, they will.
HH: What’s the boot time like when you take the regeneration into consideration?
RP: Satya takes about as much time to boot as a standard OS, 30 to 60 seconds depending on BIOS POST settings and hardware. But unlike a standard OS, boot time won’t degrade over time.
HH: How does Satya differ from the standard fork of Tails?
RP: The concept for now is Tails with more curated apps, custom wizards, control panel and contextual helpers. It lets you do a little bit more while sporting a more modern interface; our focus is really on simplifying infosec UX and the vast majority of our user’s Threat Model is less stringent than Tail’s “life or death” one.
Satya is not as paranoid as Tails is: For instance, you can very well decide to start it without connecting to Tor, by just connecting to a VPN, or even connecting directly to the internet (if you’re going to be connecting to your bank, do some online shopping or logging in to your office’s intranet, you might not always want to be appearing to be coming from another location).
Satya handles the integration with the hardware write-protection, it will ask the user to deactivate it during the OS updating process and will warn and block the user if it’s been deactivated when it shouldn’t have.
HH: Do you have a roadmap for Satya that you can reveal? Any major features or concepts?
IDM: We’d like to contribute resources to help get AppArmor operational in Tails since everyone would benefit from that. We really enjoyed Joanna Rutkowska’s talk last December at C3C on the Stateless laptop. We’re also following Qubes and Subgraph closely. Who knows, SilentKeys could end up running either one of those in a year or two… 🙂 User data being fully isolated and safe on a separate storage device and instances living in RAM disk we can imagine many interesting reimaging scenarios… We expect many fascinating suggestions from the community! 🙂
During the initial prototyping stage, we even toyed with the idea of having Whonix auto-launch its vbox instance within the host OS via the SilentKeys power button, but chose to stick with Tails because we really wanted to stick with an isolated and independent technical model and we believe it’s safer not having to rely on any host OS.
HH: Is Satya going to be available to use outside of SilentKeys?
RP: Yes, build-it-yourself SK for the hyper paranoid can use Satya, and it’s not very hard to do a non-SK version that will have Tails-style persistence on the USB
HH: I would absolutely love to get involved, are you going to be accepting code contributions via GitHub?
RP: That’s great! Yes, GitHub or we might spend the extra hours to host an OpenProject instance. For now, we’re keeping things in-house but closer to launch day we will unveil all the contributing infrastructures and tools a sane open-source project needs.
HH: How did you choose the name of Satya? Why not Silent/Silence or something linked to the product name?
RP: Well initially it was SilentOS, until last October when one morning SilentCircle came out with the term for one of their product. We’re glad actually, we ended up liking Satya more: it doesn’t sound technical, it means Truth in Sanskrit which echoes our commitment to openness and, as you’ve guessed, we savor the cheekiness…
HH: Anything to do with a certain CEO and a sense of irony? ;- )
IDM: Let’s just say the guys LOLed real hard when I included it in my alternative names list. I was sold. 😉
HH: What applications ship by default in Satya on SilentKeys?
We’re not at liberty to answer that right now as we’re still testing and auditing their chattiness and readiness but as a start all the ones in Tails are included.
HH: What software, devices and OS do you use on a daily basis? What’s your workflow and average schedule look like? Any particularly impressive “devops” workflows you’ve setup? How do you stay secure? And how is this translating to SilentKeys as a product?
RP: Debian here. Laptop only, console windows and text editors opened all day. Pretty much standard state of the art as far as devops go. We stay secure by keeping all our work on our self-hosted secured intranet and not leaking anything on the cloud. All the extra-sensitive stuff is handled on offline processes. We’ve been following up on all the Bitcoin startups, as we recon they most liken our security needs: Online-banking levels of security, on a startup budget.
HH: Do you believe in “dogfooding” by using what you create? Are you hardcore SilentKeys users yourselves?
IDM: We use 100 % FLOSS for all company and project development. We use Tails individually in the same way we will use SilentKeys when it’s out, but keep in mind we’re geeks, our computers are already pretty secure. We use Enigmail, Tox, OTR and OnionShare daily, they’ll be included in Satya. We’ll humbly say that SilentKeys will really shine in the eyes of non-technical people as an all-in-one privacy add-on to their computer. Technical folks will be able to tweak, fork and reflash the OS to their likings to leverage the hardware the way they see it fit.
Internally we’ve got a hard ‘no-cloud’ policy. Any useful tool we need, we spend the extra 6 hours (and save the extra $5-$10 monthly fee) to set up the self-hosted open-source alternative: OwnCloud instead of Dropbox and Google Docs, RocketChat instead of Slack, GNU social for an internal-twitter. It’s all automatically backed-up, encrypted and sent offsite. From day one, all the extremely sensitive stuff (like handling our master signing keys) are done offline (on a computer with no network capabilities) and backed-up offline, and we try to have as little sensitive stuff as possible.
On the public side, we have a ‘no-third parties’ policy: Piwik instead of Google Analytics, Discourse instead of Disqus, we send out our newsletter on our own, etc. The only exception to that came from our marketing advisors and is the temporary ad-campaign cookie we may send out to visitors who don’t have DoNotTrack enabled, or an ad-blocker, or those who still have not opted out at the bottom of our page. The only “sin” that has been committed in Preevio’s lifetime is using CloudFlare for free SSL, before Let’s Encrypt went live, but that’s all forever in the past now 🙂 Our friends at Gandi host our public web servers: Christophe who’s in charge of security there swore to us that there’s no shady business going on there, and that’s really the best we can do for now!
HH: What have you done to make the SilentKeys hardware and software tamper-proof?
IDM: Hardware: Tamper-proofing hardware is complicated stuff. Our design goal for the consumer version was to prevent stealthy access to the electronics inside SilentKeys. This is why the shell itself is tamper-proof aluminum and the top-facing frame and keys are tamper-evident.
This means that they cannot be removed without the maneuver leaving visible tampering traces of bending and prying, or even mount mechanism destruction for the keys.
RP: Software: The write-protection physically saves the OS from unpatched vulnerabilities that can gain root access, and our free OS updates will patch vulnerabilities as soon as they are found and fixed. Can software ever be tamper-proof on a write-enabled medium? We’ll be honest and say we doubt it but we went for the next best thing, ephemeral live OS sessions coupled with hardware write protection. These are two very solid security features currently lacking on consumer computing products. ChromeOS does a bit of read-only protection but it’s software-based. And it’s Google, meaning it’s a US government product.
HH: Do you feel that Tor still safe to use? What about the rumblings in regards to the NSA having compromised multiple exit nodes?
RP: The problem is the concept of exit-nodes as a whole: from day one they’ve been a potential weak point since they can see and manipulate traffic going out to the clear net, and it is expected that the NSA or similar would want to exploit that weakness. Tor is a great tool, a clever compromise between clear and deep Web but this cross-compatibility implies some weaknesses which I2P, for instance, doesn’t have. That being said, I2P is much more technical and hardcore: my mom wouldn’t see the point of using it.
IDM: It’s not as if Tor traffic analysis and correlation / timing attacks were cheap, automated or mass-applicable. This much sophistication in surveillance implies it becomes targeted surveillance, and as such costs money to the snoopers, meaning it probably needs to be accounted for by surveillance agencies.
All in all, with HTTPS slowly becoming the norm everywhere and making clear web DPI costlier, we still think the Tor Network is a solid and much needed addition to everyone’s safety and anonymity online. And remember, onion sites are always safe from bad exit nodes, that’s why we host one, and so should you. 🙂
HH: Do you see SilentKeys as a privacy-conscious consumer purchase or more of a professional one? Do you see it being more of an executive-level piece of hardware within a business, or something that even low-level employees should be using to combat corporate espionage and malware? Will grandma be able to appreciate the genius of SilentKeys? Will the average teen or adult?
IDM: I’ll be honest, positioning SilentKeys commercially is a bit tricky but really we kept in mind our many privacy-conscious yet technophobic relatives while building it. We want to get it out to consumers who don’t know what an ISO image is. We’re aiming for grandma-friendliness for the most important features: ease-of-use, first set-up, browsing and file storage. We also think very small businesses that don’t have the resources to hire a full IT team to secure their machines will find SilentKeys useful.
Corporate use is definitely something we think about though combating espionage really starts at the infrastructure, access permissions and GPO level, not at the endpoint, unless it’s an inside job. Which is something that happened to me (see my keyloggers blog post)
HH: Are there any other grassroots initiatives such as Let’s Encrypt and Open Net that you would like to highlight?
IDM: Policy-wise (and we know that’s where major societal changes happen, technical solutions like ours are only one part of the answer) we use LE on our website and support EFF and FSF as well as La Quadrature du Net, Framasoft, April and Nos Oignons here in France.
We’ll also take the opportunity to say we’re big fans of Tox, Bitmessage, Bitcoin, OwnCloud, Lima, OpenBazaar and HornetQ, amongst others.
HH: Are we slowly inching towards Linux/*nix becoming ubiquitous with mainstream acceptance and usage of it?


IDM: Well, Apple and Microsoft are certainly firmly in place and have their own closed ecosystem in the making. UWP sounds wonderful until you realize the implications. Paradoxically, mobile computing, gaming and the Web are forcing all actors to play nice with each other through the use of “open” and universal standards. HTML5 and Vulkan are good examples. I think Linux and derivatives will keep growing both in applications and user base under various names and devices, with people forgetting it’s actually mostly Linux bits running everything in their lives.
HH: SilentKeys ships with a dice inside the tamper-proof package, what’s the story behind that? Truly random password generation?
IDM: If I had doubts left about you possibly being a geek they’re all gone now; now I’m certain! 😉 Yes, on first use SilentKeys will play a little game with its user… 🙂
HH: Do you have any plans for further products or services following SilentKeys?
IDM: Yes, we’re hoping for success with SilentKeys as that will allow us to gather a solid team of passionate people to assist us in building a more specialized SilentKeys Pro version, a secure VOIP mobile phone/module and perhaps a computer, (stateless would rock!) which will all join SK in our “Miran” open ecosystem. We’re also thinking about services but we can’t really talk about that now. For now, we’re going to partner with ethical online service providers (e-mail, VPN and Cloud storage) to help our users switch from “You’re the product” GAFA services to more respectful companies.
HH: If you were to release a mechanical switch edition of SilentKeys, would you use Cherry MX Reds? Otherwise it wouldn’t be particularly silent! ;- )
IDM: Hehe obviously! 😉 Though I’m sure some wouldn’t mind!
HH: Do you feel that SilentKeys will open the door for people to gain an interest in programming and open-source? Although a different product category entirely, I’ve found development boards like the Raspberry Pi open the eyes of so many people to the concept of tinkering with their OS and actually caring about what it is that they’re using in terms of privacy and security.
RP: Open source absolutely, both SilentKeys and ourselves are evangelists. Programming perhaps but that’s not our focus with this project.
HH: What’s your general opinion on whether or not people care about their privacy? I personally cringe at how much information people divulge through the likes of Facebook, tracking cookies, and general data-mining through free services offered by companies like Google.
IDM: Cringe is the right word indeed. The Privacy Economy is very small and this is part of the challenge for us in coming up with SilentKeys. People assume security and privacy have no value, that they’re naturally built-in. But when one buys an unfurnished flat they usually buy curtains and change the locks. When people walk in the street they don’t expect someone or a camera stalking their every movement, glances and hesitations as they go window licking and later have that info being sold to marketers.
RP: I think it’s important to differentiate between voluntary giving up private info on Facebook and being tracked everywhere by Criteo or Google Ads. One is done in full acceptance, the other is insidious and not very moral. Google algorithms reading and parsing private e-mails is crazy; people would never let the post office read their snailmail and sell the info afterwards. Insane is the European law about websites having to inform people they use cookies and the only option is to accept. There’s a lot of madness and schizophrenia on the Web, and the shrinks can’t be heard!
HH: What’s your opinion on surveillance and privacy-invasion around the world? Any specific laws/bills or proposed government policies that you would like to draw everybody’s attention towards?
IDM: Max Schrems’s work on the US/EU Transatlantic agreement’s data retention laws is very important. Apart from that it’s all quite depressing really. The UK’s IPB law is scary. The FBI’s attempt at forcing Apple to comply was very Soviet-esque. Over here, under the pretense of being victim to two terrorist attacks last year, the French government, in a mediocre replay of the Patriot Act, has shown worrying signs of hostility towards freedom-promoting policies and technologies. A ban on public WiFi and Tor was asked for by the Interior Minister back in December. Black Boxes are being installed in many undersea cable stations, Datacenters and ISP technical facilities.

“Terrorist” and “Islamist” websites are being officially censored through IP blacklisting which, as much I as I morally condone them (see our blogpost), I think sets a dangerous precedent. I understand they want to show action and results to voters but I can hardly agree with the method. And it doesn’t solve anything: for a motivated individual it’s easy to circumvent geographical blacklisting… There’s no oversight and much broader and vital societal topics such as economic policy, unionism, encryption, foreign policy talk, activism and ecology could later be labeled or interpreted as terrorist, as menaces to stability or prosperity or extremism etc… Just look at China’s Great Firewall.
HH: It’s been a pleasure chatting with you, we’ll be looking forward to reviewing SilentKeys upon launch. You can back the SilentKeys keyboard on Kickstarter now, and you can grab an early-bird discount by subscribing to their email newsletter here.
IDM: Thanks for having us, it’s a pleasure talking with someone who knows what we deal with. Clever and thoughtful questions on all the different aspects and implications of our work, we really enjoyed the challenge! 🙂




Like this article? Share with your friends!